9 min to read
An Introduction to Cybersecurity, Capture the Flag Contests, and Basic Security Concepts
Learning web security can feel scary. Start here.
Cybersecurity is important, there’s no dodging that fact. It is also nothing like the hacking that is shown in most popular media.
However, that does not mean it isn’t interesting, it is undoubtedly so. Due to this intrigue, lots of people want to dip their feet into cybersecurity, myself included, and I have found capture the flag events (CTFs) to be a wonderful way to get a taste of the field.
Now, by no means are CTFs completely accurate in the day-to-day work of a cybersecurity professional but they are very educational and they do help people develop their cybersecurity skillsets, as well as just being fun to participate in.
In addition, if you are a programmer, these will give you an insight into the way you should design your programs so that they are not vulnerable to malevolent users. You don’t want to be the person that stored all their passwords in plain text.
What Is a CTF?
At this point, you may be asking yourself: “Cool, but what is a CTF?”
Essentially, it is a team cybersecurity competition of which there are three main types:
-
Jeopardy:** **These have a collection of tasks in several distinct categories: web exploits, binary exploitation, reverse engineering, forensics, and cryptography. By solving these challenges, you find “flags” which typically follow a standard format like flag{Th1s_1s_a_flag}. Some examples include picoCTF and Defcon CTF’s qualification round.
-
Attack-Defense: In attack-defense competitions, each team is given their own host or service and is tasked with protecting that host from other teams while also trying to exploit other teams’ hosts. Famously, the Defcon CTF final takes this format.
-
Mixed:** **As can be inferred by the name of this type of competition, it is some sort of combination of jeopardy and attack-defense competitions.
In this article, I will be mainly focusing on the jeopardy-type CTF. In the future, I may write another article on attack-defense competitions.
What Are All Those Categories?
Before you get into all of the cool categories in jeopardy contests that I mentioned earlier, you need to learn the basics. Most importantly, you need to familiarize yourself with the Linux terminal.
Here are a couple of commands that you will use over, and over, and over again:
ls: This command lists out all the files and subdirectories that you are currently in.
pwd: This prints your current working directory. If you are in the documents directory, this will return documents.
cd: This command changes the directory into any of the subdirectories of the current directory. Eg: If you have an essays folder in your documents folder and your current directory is documents, cd essays, will take you to your essays folder.
These are the absolute basics for the Linux terminal and there are a lot more commands that we will cover in the rest of this article.
To succeed in CTFs, it is also important to know:
-
A scripting language, most popular of which is Python. There are a lot of cool libraries for cybersecurity in Python, including pwn which has a lot of functions that are helpful for CTFs.
-
Number bases. Having an understanding of how this works is very helpful.
-
JavaScript: Doing good work in web exploitation needs knowledge of JavaScript as well as some SQL for SQL injections.
-
It is also advisable to have a UNIX-based operating system because of all the amazing tools that are readily available on Linux, this can be done in a virtual box, no changing your main OS necessary. However, you can still participate in CTFs on Windows.
Time to start digging into some heavier stuff.
Cryptography
Cryptography challenges consist of exactly what you think they would, codebreaking. Given a ciphertext, can you decode it into the original message? Can you do the opposite?
These types of problems include an encrypted message that you have to decrypt. To prepare for these, it is best to learn different types of ciphers and how to decrypt them.
Here are some common methods of encryption in these challenges: Caesar Ciphers, Vigenère Ciphers, and RSA. For more info on how to decrypt these, check out this link.
Steganography
Steganography is not cryptography by definition but it does involve hiding messages in plain sight. As a result, many CTF organizers will include steganography challenges in the cryptography section.
Steganography consists of hiding messages in media files, typically audio and images. It is important to note that there aren’t a lot of real applications in the field of cybersecurity with steganography, other than just increasing your knowledge.
There is a multitude of ways to do this and not enough space in this general-purpose article to cover them all, so here is an in-depth article about steganography: CTF Tidbits: Part 1 — Steganography I have been asked by a few folks what tools I use for CTF’s. What I use all depends on what the CTF is. There are all…medium.com
Binary Exploitation
Binary exploitation involves finding vulnerabilities in a program, typically Linux executables, and then exploiting these vulnerabilities to obtain the flag.
These exploitations usually involve either using the program to gain control of a shell or just modifying the program to yield the flag. This is an extremely broad field and some helpful tips can be found here.
Forensics
Forensics challenges in CTFs typically have the following aspects:
-
File format analysis: Given various files that have something wrong with them, can you fix them? Can you fix a corrupt file to produce a flag?
-
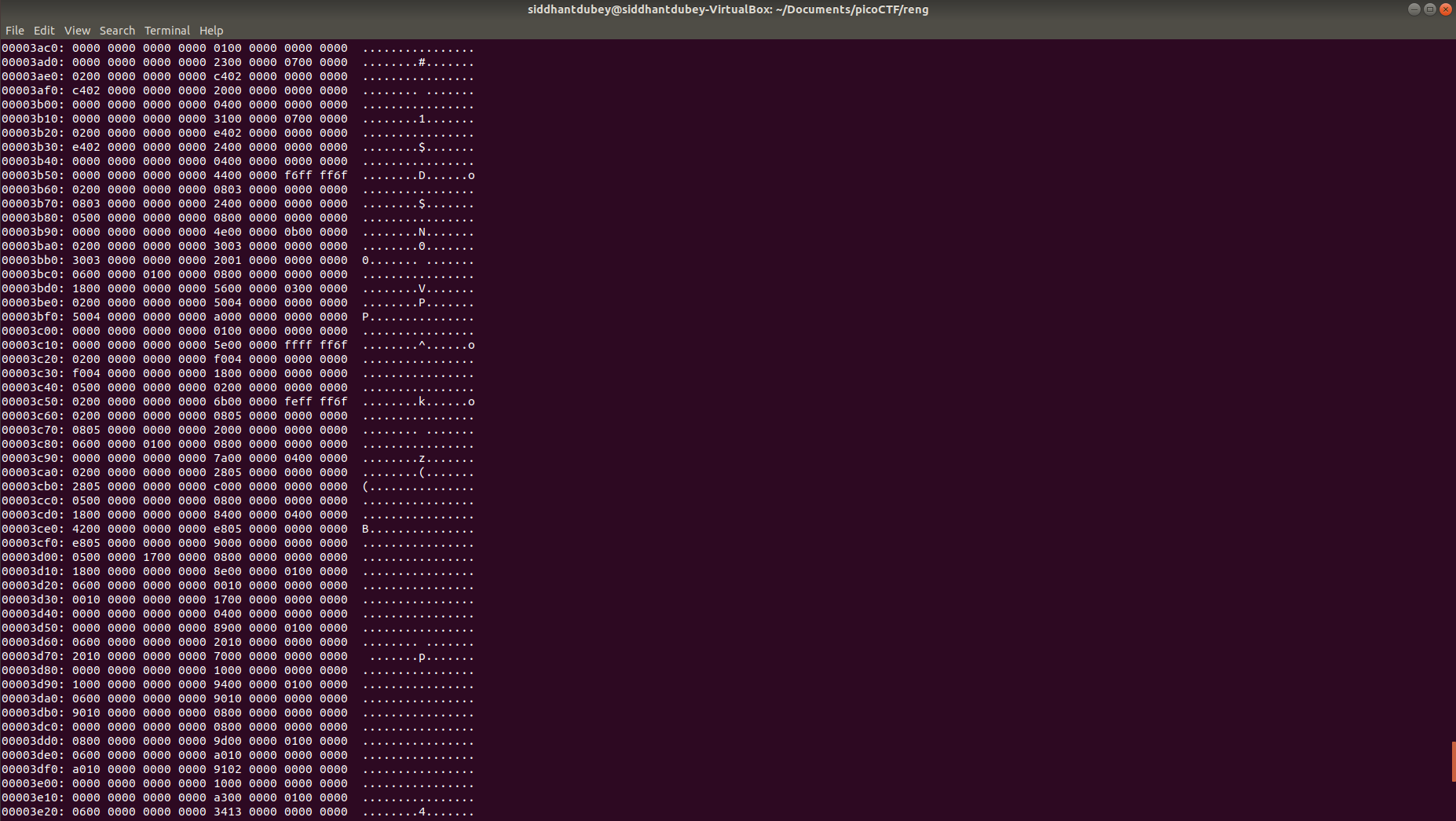
Memory dump analysis: Taking a look at the memory of the system and seeing if any important information can be learned.
-
Steganography: Yes, steganography appears in the forensics section as well.
-
Packet capture analysis: A packet is a segment of data sent from one device to another device over a network. A lot of information can be gleaned from packets and there are a lot of programs for packet analysis and capture out there. Possibly the most popular is Wireshark.
Here is something that goes into a lot of detail on this topic.
Web Exploitation
Web exploitation challenges have the contestant retrieve the flag from exploiting websites and web apps. There are a couple of ways to do this:
-
SQL injections: Sometimes, the creator of a web app unintentionally makes it so that SQL code can be inputted. This provides a golden opportunity for the exploiter to use SQL to obtain information from the databases of the web app.
-
Just inspecting element: In the easier stages of contests, event organizers may just hide flags in the HTML of the website. They may also have a JavaScript function that needs to take in a certain input to spit out the flag, these can be done with inspect element and some problem-solving skills.
-
Directory traversal: If an application takes in a directory as input and this input is not properly checked, the attacker can mess with the directories to their heart’s desire.
-
XSS (cross-site scripting): This is when the attacker can send JavaScript that will be executed by the browser of another user of the web app.
-
Command injection: Sometimes, developers forget to properly check for input that goes into a system’s shell. If not properly checked, the attacker can send whatever system commands they want to the web app.
For more in-depth information on the above topics, take a look at this wonderful resource.
Reverse Engineering
As the name suggests, these types of challenges are based around reverse-engineering a program to figure out how to properly exploit it. The product of a successful exploit is the flag, as desired.
These could be given in many programming languages but the following, especially the first two, tend to show up more than others:
-
Assembly: Reading this, you may be thinking that nobody codes in Assembly, on the contrary, quite a lot of people do. It is not extremely widespread but it used in the programming of embedded microsystems which are very relevant. This may be a bummer to learn but it is a fairly useful skill to know.
-
C: Lots of programs are written in C and its control over memory allocation makes it a valuable programming language. Familiarity with C may help you do well in reverse engineering programs written in C.
-
Java: Java is a very popular programming language and has easily-readable code. Knowing Java will help you reverse engineer it tremendously so learning it if you don’t already know it is recommended.
It is to be noted that there are a lot of times where you are not given the actual source code of the program and are just given the executable.
To overcome this hurdle, we use *decompilers. *These programs try to convert the executable back into source code.
A great example of a decompiler is Ghidra which was created by the NSA. It is a very powerful tool and very good at it what it does. It would be advisable to have set this up on your computer.
For a more in-depth explanation of reverse engineering, take a look at this wonderful resource.
Beginner-Friendly CTFs
Alright, these CTF things seem cool, how do I participate in one?
Well, future pwner, here’s a list of CTFs that are great for beginners. Note, not all of them are available right now:
Now, get out there and capture those flags. Trust me, it is an incredible experience.
A Giant List of Resources
-
Trail of bits: Lots of good information on CTFs.
Comments